Debian for STM32MP1
I bought a STM32MP1 dev board because it has a gigabit NIC with 1588 PTP timestamps as well as hardware timers that can timestamp PPS events without interrupt latency and jitter. I am hoping that it will both be better than the Beaglebone's hardware timestamps as well as at least as good network timestamps as the APU2.
I tried out STM's Yocto/OpenEmbedded based distro, but I wanted to use an existing package system that would publish their own security updates. So I started with Digikey's Debian install instructions.
Instead of building u-boot and the kernel on my own, I used the one from STM's OpenEmbedded build. The Debian sdcard image I built is here.
I put a sdcard in my STM32MP1 board and set the dip switches boot0 and boot2 (on the back) to off. This puts the board into USB DFU bootloader mode. The USB-C connector next to the HDMI port connects to the system, and I used ST's flashing tool to write the sdcard image:STM32_Programmer_CLI -c port=usb1 -w sdcard-stm32mp157a-dk1.tsv
After writing the image, I set boot0/boot2 back to on and let it boot up. I resized the root filesystem to use the entire card: resize2fs /dev/mmcblk0p4
The default user/pass is debian/temppwd. If you're using this image, change that password before connecting the system to the network. The USB micro port on the side of the board is a ST-Link connection, which includes a serial port for the console. This also comes in handy if you need to get access to u-boot/extlinux.
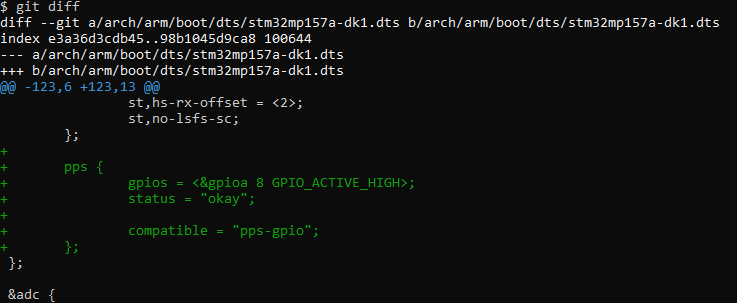
The OpenEmbedded build has a 4.19.9 kernel and it's missing a few things. I rebuilt their 4.19.49 kernel, added USB serial and pps-gpio, and removed a few unimportant things. I also changed the dts to have a pps-gpio on pin PA8.
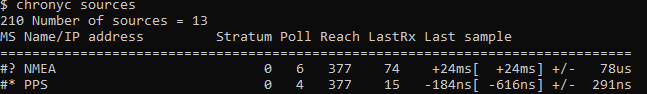
Setting up chrony with the PPS gives acceptable results:
Next up: write a kernel driver to use the hardware PPS timestamping.
Additional info
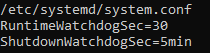
u-boot turns on the hardware watchdog, so I had to have systemd keep the watchdog alive as well:
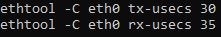
I wanted the minimum coalesce settings to lower network latency.
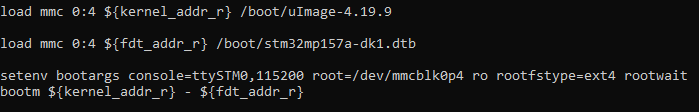
If you need to boot a kernel by hand from the u-boot command line, I used these commands:
Next article
Next: Setting up a NTP server
Questions? Comments? Contact information